Para crear nuestro propio servidor mastodon necesitamos 2 cosas:
– Un dominio propio como mastodon.piensoluegoinstalo.com
– Un host, es decir un ordenador o vps que este siempre encendido y online.
En este ejemplo y como siempre vamos a usar un centos7 y lo primero es instalar docker y docker compose.
1. Instalar Docker y Docker-Compose
yum install -y yum-utils yum-config-manager --add-repo https://download.docker.com/linux/centos/docker-ce.repo yum install docker-ce docker-ce-cli containerd.io -y systemctl start docker systemctl status docker systemctl enable docker curl -L "https://github.com/docker/compose/releases/download/v2.13.0/docker-compose-linux-x86_64" -o /usr/local/bin/docker-compose chmod +x /usr/local/bin/docker-compose docker-compose --version
2. Generar Certificados SSL
Vamos a crearlo todo dentro de un directorio docker–server dentro generamos el archivo docker–compose.yml
mkdir docker-server cd docker-server vi docker-compose.yml
Configuracion docker-compose.
version: "3.8"
services:
nginx:
container_name: nginx
image: nginx:latest
restart: unless-stopped
ports:
- 80:80
- 443:443
volumes:
- ./nginx/conf:/etc/nginx/conf.d
- ./certbot/conf:/etc/nginx/ssl
- ./html:/var/www/html
networks:
- internal_network
- external_network
mastodoncertbot:
container_name: mastodoncertbot
image: certbot/certbot:latest
command: certonly --webroot --webroot-path=/var/www/html --email adriandepalma@hotmail.es --agree-tos --no-eff-email -d mastodon.piensoluegoinstalo.com
volumes:
- ./certbot/conf:/etc/letsencrypt
- ./certbot/logs:/var/log/letsencrypt
- ./html/mastodon:/var/www/html
networks:
- internal_network
- external_network
networks:
external_network:
driver: bridge
internal_network:
internal: true
Creamos el directorio de configuracion de nginx.
mkdir nginx cd nginx mkdir conf cd conf vi default.conf
Configuracion de servidor nginx
server {
listen [::]:80;
listen 80;
server_name mastodon.piensoluegoinstalo.com;
root /var/www/html/mastodon;
}
docker logs nginx docker logs mastodoncertbot cd ./certbot/conf/live
Ahora ya tenemos los certificados firmados para mastodon.piensoluegoinstalo.com
3. Crear un servidor de mail
Ahora vamos a crear un contenedor con postfix+imap necestiamos tener un servidor de correo para enviar y recibir mail totalmente funcional.
Modificamos el docker–compose añadiendo el servidor de correo y comentando el mastodoncertbot pues solo lo usaremos a la hora de renovar o crear el certificado.
También tenemos que añadir un archivo con las variables de entorno para configurar el servidor de correo.
version: "3.8"
services:
nginx:
container_name: nginx
image: nginx:latest
restart: unless-stopped
ports:
- 80:80
- 443:443
volumes:
- ./nginx/conf:/etc/nginx/conf.d
- ./certbot/conf:/etc/nginx/ssl
- ./html:/var/www/html
networks:
- internal_network
- external_network
# mastodoncertbot:
# container_name: mastodoncertbot
# image: certbot/certbot:latest
# command: certonly --webroot --webroot-path=/var/www/html --email adriandepalma@hotmail.es --agree-tos --no-eff-email -d mastodon.piensoluegoinstalo.com
# volumes:
# - ./certbot/conf:/etc/letsencrypt
# - ./certbot/logs:/var/log/letsencrypt
# - ./html/mastodon:/var/www/html
# networks:
# - internal_network
# - external_network
mailserver:
image: docker.io/mailserver/docker-mailserver:latest
container_name: mailserver
hostname: mail
domainname: mastodon.piensoluegoinstalo.com
env_file: mailserver.env
ports:
- "25:25"
- "143:143"
- "587:587"
- "993:993"
volumes:
- ./certbot/conf:/tmp/certs
- ./html:/var/www/html
- ./mail/dms/mail-data/:/var/mail/
- ./mail/dms/mail-state/:/var/mail-state/
- ./mail/dms/mail-logs/:/var/log/mail/
- ./mail/dms/config/:/tmp/docker-mailserver/
- /etc/localtime:/etc/localtime:ro
environment:
- ENABLE_SPAMASSASSIN=1
- SPAMASSASSIN_SPAM_TO_INBOX=1
- ENABLE_CLAMAV=1
- ENABLE_FAIL2BAN=1
- ENABLE_POSTGREY=1
- ENABLE_SASLAUTHD=0
- ONE_DIR=1
cap_add:
- NET_ADMIN
restart: always
networks:
- internal_network
- external_network
deploy:
resources:
limits:
cpus: '0.50'
memory: 1024M
reservations:
cpus: '0.25'
memory: 512M
networks:
external_network:
driver: bridge
internal_network:
internal: true
Creamos el archivo con las variables de entorno mailserver.env
# ----------------------------------------------- # --- Mailserver Environment Variables ---------- # ----------------------------------------------- # DOCUMENTATION FOR THESE VARIABLES IS FOUND UNDER # https://docker-mailserver.github.io/docker-mailserver/edge/config/environment/ # ----------------------------------------------- # --- General Section --------------------------- # ----------------------------------------------- # empty => uses the `hostname` command to get the mail server's canonical hostname # => Specify a fully-qualified domainname to serve mail for. This is used for many of the config features so if you can't set your hostname (e.g. you're in a container platform that doesn't let you) specify it in this environment variable. OVERRIDE_HOSTNAME= # REMOVED in version v11.0.0! Use LOG_LEVEL instead. DMS_DEBUG=0 # Set the log level for DMS. # This is mostly relevant for container startup scripts and change detection event feedback. # # Valid values (in order of increasing verbosity) are: `error`, `warn`, `info`, `debug` and `trace`. # The default log level is `info`. LOG_LEVEL=info # critical => Only show critical messages # error => Only show erroneous output # **warn** => Show warnings # info => Normal informational output # debug => Also show debug messages SUPERVISOR_LOGLEVEL= # 0 => mail state in default directories # 1 => consolidate all states into a single directory (`/var/mail-state`) to allow persistence using docker volumes ONE_DIR=1 # **empty** => use FILE # LDAP => use LDAP authentication # OIDC => use OIDC authentication (not yet implemented) # FILE => use local files (this is used as the default) ACCOUNT_PROVISIONER= # empty => postmaster@domain.com # => Specify the postmaster address POSTMASTER_ADDRESS=postmaster@mastodon.piensoluegoinstalo.com # Check for updates on container start and then once a day # If an update is available, a mail is sent to POSTMASTER_ADDRESS # 0 => Update check disabled # 1 => Update check enabled ENABLE_UPDATE_CHECK=1 # Customize the update check interval. # Number + Suffix. Suffix must be 's' for seconds, 'm' for minutes, 'h' for hours or 'd' for days. UPDATE_CHECK_INTERVAL=1d # Set different options for mynetworks option (can be overwrite in postfix-main.cf) # **WARNING**: Adding the docker network's gateway to the list of trusted hosts, e.g. using the `network` or # `connected-networks` option, can create an open relay # https://github.com/docker-mailserver/docker-mailserver/issues/1405#issuecomment-590106498 # The same can happen for rootless podman. To prevent this, set the value to "none" or configure slirp4netns # https://github.com/docker-mailserver/docker-mailserver/issues/2377 # # none => Explicitly force authentication # container => Container IP address only # host => Add docker container network (ipv4 only) # network => Add all docker container networks (ipv4 only) # connected-networks => Add all connected docker networks (ipv4 only) PERMIT_DOCKER=connected-networks # Set the timezone. If this variable is unset, the container runtime will try to detect the time using # `/etc/localtime`, which you can alternatively mount into the container. The value of this variable # must follow the pattern `AREA/ZONE`, i.e. of you want to use Germany's time zone, use `Europe/Berlin`. # You can lookup all available timezones here: https://en.wikipedia.org/wiki/List_of_tz_database_time_zones#List TZ= # In case you network interface differs from 'eth0', e.g. when you are using HostNetworking in Kubernetes, # you can set NETWORK_INTERFACE to whatever interface you want. This interface will then be used. # - **empty** => eth0 NETWORK_INTERFACE= # empty => modern # modern => Enables TLSv1.2 and modern ciphers only. (default) # intermediate => Enables TLSv1, TLSv1.1 and TLSv1.2 and broad compatibility ciphers. TLS_LEVEL= # Configures the handling of creating mails with forged sender addresses. # # empty => (not recommended, but default for backwards compatibility reasons) # Mail address spoofing allowed. Any logged in user may create email messages with a forged sender address. # See also https://en.wikipedia.org/wiki/Email_spoofing # 1 => (recommended) Mail spoofing denied. Each user may only send with his own or his alias addresses. # Addresses with extension delimiters(http://www.postfix.org/postconf.5.html#recipient_delimiter) are not able to send messages. SPOOF_PROTECTION= # Enables the Sender Rewriting Scheme. SRS is needed if your mail server acts as forwarder. See [postsrsd](https://github.com/roehling/postsrsd/blob/master/README.md#sender-rewriting-scheme-crash-course) for further explanation. # - **0** => Disabled # - 1 => Enabled ENABLE_SRS=0 # 1 => Enables POP3 service # empty => disables POP3 ENABLE_POP3= ENABLE_CLAMAV=0 # Amavis content filter (used for ClamAV & SpamAssassin) # 0 => Disabled # 1 => Enabled ENABLE_AMAVIS=0 # -1/-2/-3 => Only show errors # **0** => Show warnings # 1/2 => Show default informational output # 3/4/5 => log debug information (very verbose) AMAVIS_LOGLEVEL=0 # This enables the [zen.spamhaus.org](https://www.spamhaus.org/zen/) DNS block list in postfix # and various [lists](https://github.com/docker-mailserver/docker-mailserver/blob/f7465a50888eef909dbfc01aff4202b9c7d8bc00/target/postfix/main.cf#L58-L66) in postscreen. # Note: Emails will be rejected, if they don't pass the block list checks! # **0** => DNS block lists are disabled # 1 => DNS block lists are enabled ENABLE_DNSBL=0 # If you enable Fail2Ban, don't forget to add the following lines to your `docker-compose.yml`: # cap_add: # - NET_ADMIN # Otherwise, `nftables` won't be able to ban IPs. ENABLE_FAIL2BAN=0 # Fail2Ban blocktype # drop => drop packet (send NO reply) # reject => reject packet (send ICMP unreachable) FAIL2BAN_BLOCKTYPE=drop # 1 => Enables Managesieve on port 4190 # empty => disables Managesieve ENABLE_MANAGESIEVE= # **enforce** => Allow other tests to complete. Reject attempts to deliver mail with a 550 SMTP reply, and log the helo/sender/recipient information. Repeat this test the next time the client connects. # drop => Drop the connection immediately with a 521 SMTP reply. Repeat this test the next time the client connects. # ignore => Ignore the failure of this test. Allow other tests to complete. Repeat this test the next time the client connects. This option is useful for testing and collecting statistics without blocking mail. POSTSCREEN_ACTION=enforce # empty => all daemons start # 1 => only launch postfix smtp SMTP_ONLY= # Please read [the SSL page in the documentation](https://docker-mailserver.github.io/docker-mailserver/edge/config/security/ssl) for more information. # # empty => SSL disabled # letsencrypt => Enables Let's Encrypt certificates # custom => Enables custom certificates # manual => Let's you manually specify locations of your SSL certificates for non-standard cases # self-signed => Enables self-signed certificates SSL_TYPE=manual # These are only supported with `SSL_TYPE=manual`. # Provide the path to your cert and key files that you've mounted access to within the container. SSL_CERT_PATH=/tmp/certs/live/mastodon.piensoluegoinstalo.com/fullchain.pem SSL_KEY_PATH=/tmp/certs/live/mastodon.piensoluegoinstalo.com/privkey.pem # Optional: A 2nd certificate can be supported as fallback (dual cert support), eg ECDSA with an RSA fallback. # Useful for additional compatibility with older MTA and MUA (eg pre-2015). SSL_ALT_CERT_PATH= SSL_ALT_KEY_PATH= # Set how many days a virusmail will stay on the server before being deleted # empty => 7 days VIRUSMAILS_DELETE_DELAY= # This Option is activating the Usage of POSTFIX_DAGENT to specify a lmtp client different from default dovecot socket. # empty => disabled # 1 => enabled ENABLE_POSTFIX_VIRTUAL_TRANSPORT= # Enabled by ENABLE_POSTFIX_VIRTUAL_TRANSPORT. Specify the final delivery of postfix # # empty => fail # `lmtp:unix:private/dovecot-lmtp` (use socket) # `lmtps:inet:: ` (secure lmtp with starttls, take a look at https://sys4.de/en/blog/2014/11/17/sicheres-lmtp-mit-starttls-in-dovecot/) # `lmtp: :2003` (use kopano as mailstore) # etc. POSTFIX_DAGENT= # Set the mailbox size limit for all users. If set to zero, the size will be unlimited (default). # # empty => 0 POSTFIX_MAILBOX_SIZE_LIMIT= # See https://docker-mailserver.github.io/docker-mailserver/edge/config/user-management/accounts/#notes # 0 => Dovecot quota is disabled # 1 => Dovecot quota is enabled ENABLE_QUOTAS=1 # Set the message size limit for all users. If set to zero, the size will be unlimited (not recommended!) # # empty => 10240000 (~10 MB) POSTFIX_MESSAGE_SIZE_LIMIT= # Mails larger than this limit won't be scanned. # ClamAV must be enabled (ENABLE_CLAMAV=1) for this. # # empty => 25M (25 MB) CLAMAV_MESSAGE_SIZE_LIMIT= # Enables regular pflogsumm mail reports. # This is a new option. The old REPORT options are still supported for backwards compatibility. If this is not set and reports are enabled with the old options, logrotate will be used. # # not set => No report # daily_cron => Daily report for the previous day # logrotate => Full report based on the mail log when it is rotated PFLOGSUMM_TRIGGER= # Recipient address for pflogsumm reports. # # not set => Use REPORT_RECIPIENT or POSTMASTER_ADDRESS # => Specify the recipient address(es) PFLOGSUMM_RECIPIENT= # Sender address (`FROM`) for pflogsumm reports if pflogsumm reports are enabled. # # not set => Use REPORT_SENDER # => Specify the sender address PFLOGSUMM_SENDER= # Interval for logwatch report. # # none => No report is generated # daily => Send a daily report # weekly => Send a report every week LOGWATCH_INTERVAL= # Recipient address for logwatch reports if they are enabled. # # not set => Use REPORT_RECIPIENT or POSTMASTER_ADDRESS # => Specify the recipient address(es) LOGWATCH_RECIPIENT= # Sender address (`FROM`) for logwatch reports if logwatch reports are enabled. # # not set => Use REPORT_SENDER # => Specify the sender address LOGWATCH_SENDER= # Defines who receives reports if they are enabled. # **empty** => ${POSTMASTER_ADDRESS} # => Specify the recipient address REPORT_RECIPIENT= # Defines who sends reports if they are enabled. # **empty** => mailserver-report@${DOMAINNAME} # => Specify the sender address REPORT_SENDER= # Changes the interval in which log files are rotated # **weekly** => Rotate log files weekly # daily => Rotate log files daily # monthly => Rotate log files monthly # # Note: This Variable actually controls logrotate inside the container # and rotates the log files depending on this setting. The main log output is # still available in its entirety via `docker logs mail` (Or your # respective container name). If you want to control logrotation for # the Docker-generated logfile see: # https://docs.docker.com/config/containers/logging/configure/ # # Note: This variable can also determine the interval for Postfix's log summary reports, see [`PFLOGSUMM_TRIGGER`](#pflogsumm_trigger). LOGROTATE_INTERVAL=weekly # Choose TCP/IP protocols for postfix to use # **all** => All possible protocols. # ipv4 => Use only IPv4 traffic. Most likely you want this behind Docker. # ipv6 => Use only IPv6 traffic. # # Note: More details at http://www.postfix.org/postconf.5.html#inet_protocols POSTFIX_INET_PROTOCOLS=all # Choose TCP/IP protocols for dovecot to use # **all** => Listen on all interfaces # ipv4 => Listen only on IPv4 interfaces. Most likely you want this behind Docker. # ipv6 => Listen only on IPv6 interfaces. # # Note: More information at https://dovecot.org/doc/dovecot-example.conf DOVECOT_INET_PROTOCOLS=all # ----------------------------------------------- # --- SpamAssassin Section ---------------------- # ----------------------------------------------- ENABLE_SPAMASSASSIN=0 # deliver spam messages in the inbox (eventually tagged using SA_SPAM_SUBJECT) SPAMASSASSIN_SPAM_TO_INBOX=1 # KAM is a 3rd party SpamAssassin ruleset, provided by the McGrail Foundation. # If SpamAssassin is enabled, KAM can be used in addition to the default ruleset. # - **0** => KAM disabled # - 1 => KAM enabled # # Note: only has an effect if `ENABLE_SPAMASSASSIN=1` ENABLE_SPAMASSASSIN_KAM=0 # spam messages will be moved in the Junk folder (SPAMASSASSIN_SPAM_TO_INBOX=1 required) MOVE_SPAM_TO_JUNK=1 # add spam info headers if at, or above that level: SA_TAG=2.0 # add 'spam detected' headers at that level SA_TAG2=6.31 # triggers spam evasive actions SA_KILL=6.31 # add tag to subject if spam detected SA_SPAM_SUBJECT=***SPAM***** # ----------------------------------------------- # --- Fetchmail Section ------------------------- # ----------------------------------------------- ENABLE_FETCHMAIL=0 # The interval to fetch mail in seconds FETCHMAIL_POLL=300 # ----------------------------------------------- # --- LDAP Section ------------------------------ # ----------------------------------------------- # A second container for the ldap service is necessary (i.e. https://github.com/osixia/docker-openldap) # For preparing the ldap server to use in combination with this container this article may be helpful: http://acidx.net/wordpress/2014/06/installing-a-mailserver-with-postfix-dovecot-sasl-ldap-roundcube/ # with the :edge tag, use ACCOUNT_PROVISIONER=LDAP # empty => LDAP authentification is disabled # 1 => LDAP authentification is enabled ENABLE_LDAP= # empty => no # yes => LDAP over TLS enabled for Postfix LDAP_START_TLS= # If you going to use the mailserver in combination with docker-compose you can set the service name here # empty => mail.domain.com # Specify the dns-name/ip-address where the ldap-server LDAP_SERVER_HOST= # empty => ou=people,dc=domain,dc=com # => e.g. LDAP_SEARCH_BASE=dc=mydomain,dc=local LDAP_SEARCH_BASE= # empty => cn=admin,dc=domain,dc=com # => take a look at examples of SASL_LDAP_BIND_DN LDAP_BIND_DN= # empty** => admin # => Specify the password to bind against ldap LDAP_BIND_PW= # e.g. `"(&(mail=%s)(mailEnabled=TRUE))"` # => Specify how ldap should be asked for users LDAP_QUERY_FILTER_USER= # e.g. `"(&(mailGroupMember=%s)(mailEnabled=TRUE))"` # => Specify how ldap should be asked for groups LDAP_QUERY_FILTER_GROUP= # e.g. `"(&(mailAlias=%s)(mailEnabled=TRUE))"` # => Specify how ldap should be asked for aliases LDAP_QUERY_FILTER_ALIAS= # e.g. `"(&(|(mail=*@%s)(mailalias=*@%s)(mailGroupMember=*@%s))(mailEnabled=TRUE))"` # => Specify how ldap should be asked for domains LDAP_QUERY_FILTER_DOMAIN= # ----------------------------------------------- # --- Dovecot Section --------------------------- # ----------------------------------------------- # empty => no # yes => LDAP over TLS enabled for Dovecot DOVECOT_TLS= # e.g. `"(&(objectClass=PostfixBookMailAccount)(uniqueIdentifier=%n))"` DOVECOT_USER_FILTER= # e.g. `"(&(objectClass=PostfixBookMailAccount)(uniqueIdentifier=%n))"` DOVECOT_PASS_FILTER= # Define the mailbox format to be used # default is maildir, supported values are: sdbox, mdbox, maildir DOVECOT_MAILBOX_FORMAT=maildir # empty => no # yes => Allow bind authentication for LDAP # https://wiki.dovecot.org/AuthDatabase/LDAP/AuthBinds DOVECOT_AUTH_BIND= # ----------------------------------------------- # --- Postgrey Section -------------------------- # ----------------------------------------------- ENABLE_POSTGREY=0 # greylist for N seconds POSTGREY_DELAY=300 # delete entries older than N days since the last time that they have been seen POSTGREY_MAX_AGE=35 # response when a mail is greylisted POSTGREY_TEXT="Delayed by Postgrey" # whitelist host after N successful deliveries (N=0 to disable whitelisting) POSTGREY_AUTO_WHITELIST_CLIENTS=5 # ----------------------------------------------- # --- SASL Section ------------------------------ # ----------------------------------------------- ENABLE_SASLAUTHD=0 # empty => pam # `ldap` => authenticate against ldap server # `shadow` => authenticate against local user db # `mysql` => authenticate against mysql db # `rimap` => authenticate against imap server # Note: can be a list of mechanisms like pam ldap shadow SASLAUTHD_MECHANISMS= # empty => None # e.g. with SASLAUTHD_MECHANISMS rimap you need to specify the ip-address/servername of the imap server ==> xxx.xxx.xxx.xxx SASLAUTHD_MECH_OPTIONS= # empty => Use value of LDAP_SERVER_HOST # Note: since version 10.0.0, you can specify a protocol here (like ldaps://); this deprecates SASLAUTHD_LDAP_SSL. SASLAUTHD_LDAP_SERVER= # empty => Use value of LDAP_BIND_DN # specify an object with priviliges to search the directory tree # e.g. active directory: SASLAUTHD_LDAP_BIND_DN=cn=Administrator,cn=Users,dc=mydomain,dc=net # e.g. openldap: SASLAUTHD_LDAP_BIND_DN=cn=admin,dc=mydomain,dc=net SASLAUTHD_LDAP_BIND_DN= # empty => Use value of LDAP_BIND_PW SASLAUTHD_LDAP_PASSWORD= # empty => Use value of LDAP_SEARCH_BASE # specify the search base SASLAUTHD_LDAP_SEARCH_BASE= # empty => default filter `(&(uniqueIdentifier=%u)(mailEnabled=TRUE))` # e.g. for active directory: `(&(sAMAccountName=%U)(objectClass=person))` # e.g. for openldap: `(&(uid=%U)(objectClass=person))` SASLAUTHD_LDAP_FILTER= # empty => no # yes => LDAP over TLS enabled for SASL # If set to yes, the protocol in SASLAUTHD_LDAP_SERVER must be ldap:// or missing. SASLAUTHD_LDAP_START_TLS= # empty => no # yes => Require and verify server certificate # If yes you must/could specify SASLAUTHD_LDAP_TLS_CACERT_FILE or SASLAUTHD_LDAP_TLS_CACERT_DIR. SASLAUTHD_LDAP_TLS_CHECK_PEER= # File containing CA (Certificate Authority) certificate(s). # empty => Nothing is added to the configuration # Any value => Fills the `ldap_tls_cacert_file` option SASLAUTHD_LDAP_TLS_CACERT_FILE= # Path to directory with CA (Certificate Authority) certificates. # empty => Nothing is added to the configuration # Any value => Fills the `ldap_tls_cacert_dir` option SASLAUTHD_LDAP_TLS_CACERT_DIR= # Specify what password attribute to use for password verification. # empty => Nothing is added to the configuration but the documentation says it is `userPassword` by default. # Any value => Fills the `ldap_password_attr` option SASLAUTHD_LDAP_PASSWORD_ATTR= # empty => No sasl_passwd will be created # string => `/etc/postfix/sasl_passwd` will be created with the string as password SASL_PASSWD= # empty => `bind` will be used as a default value # `fastbind` => The fastbind method is used # `custom` => The custom method uses userPassword attribute to verify the password SASLAUTHD_LDAP_AUTH_METHOD= # Specify the authentication mechanism for SASL bind # empty => Nothing is added to the configuration # Any value => Fills the `ldap_mech` option SASLAUTHD_LDAP_MECH= # ----------------------------------------------- # --- SRS Section ------------------------------- # ----------------------------------------------- # envelope_sender => Rewrite only envelope sender address (default) # header_sender => Rewrite only header sender (not recommended) # envelope_sender,header_sender => Rewrite both senders # An email has an "envelope" sender (indicating the sending server) and a # "header" sender (indicating who sent it). More strict SPF policies may require # you to replace both instead of just the envelope sender. SRS_SENDER_CLASSES=envelope_sender # empty => Envelope sender will be rewritten for all domains # provide comma separated list of domains to exclude from rewriting SRS_EXCLUDE_DOMAINS= # empty => generated when the image is built # provide a secret to use in base64 # you may specify multiple keys, comma separated. the first one is used for # signing and the remaining will be used for verification. this is how you # rotate and expire keys SRS_SECRET= # ----------------------------------------------- # --- Default Relay Host Section ---------------- # ----------------------------------------------- # Setup relaying all mail through a default relay host # # empty => don't configure default relay host # default host and optional port to relay all mail through DEFAULT_RELAY_HOST= # ----------------------------------------------- # --- Multi-Domain Relay Section ---------------- # ----------------------------------------------- # Setup relaying for multiple domains based on the domain name of the sender # optionally uses usernames and passwords in postfix-sasl-password.cf and relay host mappings in postfix-relaymap.cf # # empty => don't configure relay host # default host to relay mail through RELAY_HOST= # empty => 25 # default port to relay mail RELAY_PORT=25 # empty => no default # default relay username (if no specific entry exists in postfix-sasl-password.cf) RELAY_USER= # empty => no default # password for default relay user RELAY_PASSWORD=
Del archivo de variables de entorno archivo atentos al dominio y los certificados que son los que hemos generado en paso anterior
A continuacion vamos a usar el archivo setup.sh que nos servira para interactuar contenedor mailserver para crear cuentas de correo.
#!/bin/bash
# version v1.0.0
# executed manually / via Make
# task wrapper for various setup scripts
CONFIG_PATH=
CONTAINER_NAME=
CRI=
DEFAULT_CONFIG_PATH=
DESIRED_CONFIG_PATH=
DIR=$(pwd)
DMS_CONFIG='/tmp/docker-mailserver'
IMAGE_NAME=
DEFAULT_IMAGE_NAME='docker.io/mailserver/docker-mailserver:latest'
INFO=
PODMAN_ROOTLESS=false
USE_SELINUX=
USE_TTY=
VOLUME=
WHITE=$(echo -ne '\e[37m')
ORANGE=$(echo -ne '\e[38;5;214m')
LBLUE=$(echo -ne '\e[94m')
RESET=$(echo -ne '\e[0m')
set -euEo pipefail
shopt -s inherit_errexit 2>/dev/null || true
function _show_local_usage
{
# shellcheck disable=SC2059
printf '%s' "${ORANGE}OPTIONS${RESET}
${LBLUE}Config path, container or image adjustments${RESET}
-i IMAGE_NAME
Provides the name of the 'docker-mailserver' image. The default value is
'${WHITE}${DEFAULT_IMAGE_NAME}${RESET}'
-c CONTAINER_NAME
Provides the name of the running container.
-p PATH
Provides the local path of the config folder to the temporary container instance.
Does not work if an existing a 'docker-mailserver' container is already running.
${LBLUE}SELinux${RESET}
-z
Allows container access to the bind mount content that is shared among
multiple containers on a SELinux-enabled host.
-Z
Allows container access to the bind mount content that is private and
unshared with other containers on a SELinux-enabled host.
${LBLUE}Podman${RESET}
-R
Accept running in Podman rootless mode. Ignored when using Docker / Docker Compose.
"
[[ ${1:-} == 'no-exit' ]] && return 0
# shellcheck disable=SC2059
printf '%s' "${ORANGE}EXIT STATUS${RESET}
Exit status is 0 if the command was successful. If there was an unexpected error, an error
message is shown describing the error. In case of an error, the script will exit with exit
status 1.
"
}
function _get_absolute_script_directory
{
if dirname "$(readlink -f "${0}")" &>/dev/null
then
DIR=$(dirname "$(readlink -f "${0}")")
elif realpath -e -L "${0}" &>/dev/null
then
DIR=$(realpath -e -L "${0}")
DIR="${DIR%/setup.sh}"
fi
}
function _set_default_config_path
{
if [[ -d "${DIR}/config" ]]
then
# legacy path (pre v10.2.0)
DEFAULT_CONFIG_PATH="${DIR}/config"
else
DEFAULT_CONFIG_PATH="${DIR}/docker-data/dms/config"
fi
}
function _handle_config_path
{
if [[ -z ${DESIRED_CONFIG_PATH} ]]
then
# no desired config path
if [[ -n ${CONTAINER_NAME} ]]
then
VOLUME=$(${CRI} inspect "${CONTAINER_NAME}" \
--format="{{range .Mounts}}{{ println .Source .Destination}}{{end}}" | \
grep "${DMS_CONFIG}$" 2>/dev/null || :)
fi
if [[ -n ${VOLUME} ]]
then
CONFIG_PATH=$(echo "${VOLUME}" | awk '{print $1}')
fi
if [[ -z ${CONFIG_PATH} ]]
then
CONFIG_PATH=${DEFAULT_CONFIG_PATH}
fi
else
CONFIG_PATH=${DESIRED_CONFIG_PATH}
fi
}
function _run_in_new_container
{
# start temporary container with specified image
if ! ${CRI} history -q "${IMAGE_NAME}" &>/dev/null
then
echo "Image '${IMAGE_NAME}' not found. Pulling ..."
${CRI} pull "${IMAGE_NAME}"
fi
${CRI} run --rm "${USE_TTY}" \
-v "${CONFIG_PATH}:${DMS_CONFIG}${USE_SELINUX}" \
"${IMAGE_NAME}" "${@}"
}
function _main
{
_get_absolute_script_directory
_set_default_config_path
local OPTIND
while getopts ":c:i:p:zZR" OPT
do
case ${OPT} in
( i ) IMAGE_NAME="${OPTARG}" ;;
( z | Z ) USE_SELINUX=":${OPT}" ;;
( c ) CONTAINER_NAME="${OPTARG}" ;;
( R ) PODMAN_ROOTLESS=true ;;
( p )
case "${OPTARG}" in
( /* ) DESIRED_CONFIG_PATH="${OPTARG}" ;;
( * ) DESIRED_CONFIG_PATH="${DIR}/${OPTARG}" ;;
esac
if [[ ! -d ${DESIRED_CONFIG_PATH} ]]
then
echo "Specified directory '${DESIRED_CONFIG_PATH}' doesn't exist" >&2
exit 1
fi
;;
( * )
echo "Invalid option: '-${OPTARG}'" >&2
echo -e "Use './setup.sh help' to get a complete overview.\n" >&2
_show_local_usage 'no-exit'
exit 1
;;
esac
done
shift $(( OPTIND - 1 ))
if command -v docker &>/dev/null
then
CRI=docker
elif command -v podman &>/dev/null
then
CRI=podman
if ! ${PODMAN_ROOTLESS} && [[ ${EUID} -ne 0 ]]
then
read -r -p "You are running Podman in rootless mode. Continue? [Y/n] "
[[ -n ${REPLY} ]] && [[ ${REPLY} =~ (n|N) ]] && exit 0
fi
else
echo 'No supported Container Runtime Interface detected.'
exit 1
fi
INFO=$(${CRI} ps --no-trunc --format "{{.Image}};{{.Names}}" --filter \
label=org.opencontainers.image.title="docker-mailserver" | tail -1)
[[ -z ${CONTAINER_NAME} ]] && CONTAINER_NAME=${INFO#*;}
[[ -z ${IMAGE_NAME} ]] && IMAGE_NAME=${INFO%;*}
if [[ -z ${IMAGE_NAME} ]]
then
IMAGE_NAME=${NAME:-${DEFAULT_IMAGE_NAME}}
fi
if test -t 0
then
USE_TTY="-it"
else
# GitHub Actions will fail (or really anything else
# lacking an interactive tty) if we don't set a
# value here; "-t" alone works for these cases.
USE_TTY="-t"
fi
_handle_config_path
if [[ -n ${CONTAINER_NAME} ]]
then
${CRI} exec "${USE_TTY}" "${CONTAINER_NAME}" setup "${@}"
else
_run_in_new_container setup "${@}"
fi
[[ ${1:-} == 'help' ]] && _show_local_usage
return 0
}
[[ -z ${1:-} ]] && set 'help'
_main "${@}"
Le damos permisos de ejecución
chmod a+x setup.sh
Y creamos dos cuentas mails en nuestro servidor de correo
./setup.sh email add mastodon@mastodon.piensoluegoinstalo.com mypassword ./setup.sh email add postmaster@mastodon.piensoluegoinstalo.com mypassword
4.Configurar DMARC y DKIM
Ahora tenemos un servidor de correo, pero no es del todo funcional han de configurarse records TXT en el dominio y poner una configuración especifica que ahora vamos a generar
./setup.sh config dkim ./setup.sh config dkim domain mastodon.piensoluegoinstalo.com
Hacemos cat para ver la clave publica que tenemos que añadir al dominio como TXT.
cat ./mail/dms/config/opendkim/keys/mastodon.piensoluegoinstalo.com/mail.txt
En nuestro registrador dns vamos a necesitar 3 record TXT uno que te lo de con el mismo nombre del dominio es decir como host «mastodon.piensoluegoinstalo.com»
v=spf1 mx -all
En nuestro registrador dns vamos a necesitar 3 record TXT uno que te lo dé con el mismo nombre del dominio es decir como host «mastodon.piensoluegoinstalo.com»
v=DMARC1;p=quarantine;pct=100;rua=mailto:postmaster@mastodon.piensoluegoinstalo.com
y el ultimo que sea el dkim que responda al host mail._domainkey.mastodon.piensoluegoinstalo.com
"v=DKIM1; h=sha256; k=rsa; "
"p=MIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAu7L9fRaYBcfFMRk9HmrRySU0jIL51qTVkwFLD6Wgzaw7SGEmFdXQbUVjF5Kp07jPMs4zE84zFi1iOuyl7ST5//xUHRjRZsyBNRFljjny6jhE7JB/8BZiDWj2hR7q2is2tLoOz/XAVb8GRzplUGJQPrRkMt1kKxezKLKB+is/+eUmE7EKeruFr9347fxlrq08/PotvMfg6c8Zrl"
"PTFqf56iK9EEWwK48UK4iCbhNcQ8a74K079xOJ70UsGhe7PYdu4rKRvg/8vXDM5tO+f2Eaq6kyCsPwczfPrPXgCMOunb4Mc0JNW1G7nFf7P5JVHcdS66hxhggarb2uNNLhSoGrmqZSZZYtMIAQ2r6uuWaqtHpvWp2jSAd11PV/poxw1YB9BF3SR9ezbOq3FY75brcxja2YUPM+9CWBW3SOZpaX3XcS42PugD31Dmz9LP3thKfLaOtYn3rj"
"9ovvYGFCCs95++RTT9/A/r3JI6HKfA4SPxZjUH1J1fXLOXdgCX3C2az5A8+Kl9pI44LOIg16Zz+y0xA39D5lt2vxFo0YJAWvCns/aaGjVwCQfNBpoKotxQHs/xdUj6funtjHRCmU6Ey7zeSsfqy2Usnjr5JXBdTAv6tA8xe1Sh7bM3M5VXl8eDDGXroYw59KsGCCmq2Fvxy+jCudSfl5uBlLr94OrCM+L0sCAwEAAQ=="
Para comprobar que hemos insertado el contenido correctamente:
yum install bind-utils -y host -t txt mastodon.piensoluegoinstalo.com host -t txt _dmarc.mastodon.piensoluegoinstalo.com host -t txt mail._domainkey.mastodon.piensoluegoinstalo.com
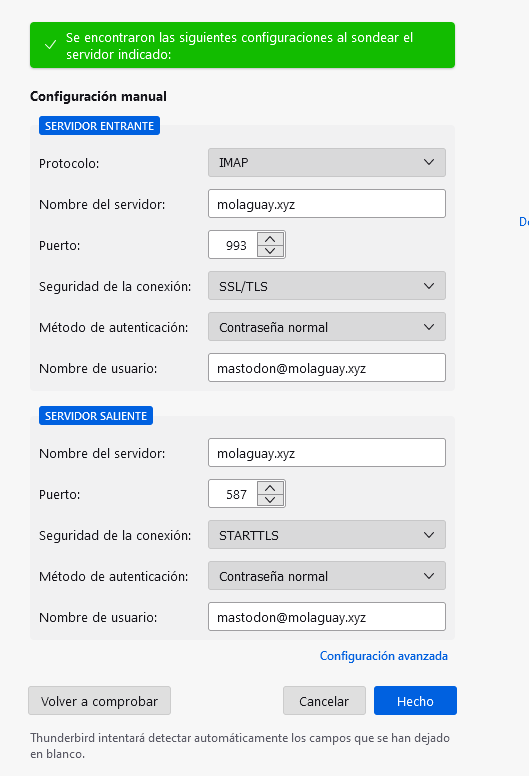
Ahora ya podemos configurar un cliente de correo y a enviar y recibir correos.
Os pego la imagen de la configuración del cliente thunderbird.
5. Desplegar Mastodon
Ahora si vamos a desplegar Mastodon que se compone de varios contenedores. Se compone de 3 tipos de bases de datos que son postgresql,redis y elasticsearch.
Creamos el archivo de variables de entorno para las bases de datos database.env
Podemos poner la password que queramos con este comando se genera una clave hexadecimal al azar.
openssl rand -hex 15
vi database.env
POSTGRES_USER=mastodon POSTGRES_DB=mastodon_production POSTGRES_PASSWORD=df519daf9236b9383c042bc25c4703 ES_JAVA_OPTS=-Xms512m -Xmx512m ELASTIC_PASSWORD=gpwETw6U875pbhnPxbo3 DB_HOST=postgresql DB_USER=mastodon DB_NAME=mastodon_production DB_PASS=df519daf9236b9383c042bc25c4703 DB_PORT=5432 REDIS_HOST=redis REDIS_PORT=6379 CACHE_REDIS_HOST=redis-volatile CACHE_REDIS_PORT=6379 ES_ENABLED=false ES_HOST=elasticsearch ES_PORT=9200 ES_USER=elastic ES_PASS=gpwETw6U875pbhnPxbo3
Ahora añadimos la los contenedores mastodon al docker compose, comentados el archivo de variables de entorno application.env porque necesitamos generar los secretos que usaremos en mastodon.
version: "3.8"
services:
nginx:
container_name: nginx
image: nginx:latest
restart: unless-stopped
ports:
- 80:80
- 443:443
volumes:
- ./nginx/conf:/etc/nginx/conf.d
- ./certbot/conf:/etc/nginx/ssl
- ./html:/var/www/html
networks:
- internal_network
- external_network
# mastodoncertbot:
# container_name: mastodoncertbot
# image: certbot/certbot:latest
# command: certonly --webroot --webroot-path=/var/www/html --email adriandepalma@hotmail.es --agree-tos --no-eff-email -d mastodon.piensoluegoinstalo.com
# volumes:
# - ./certbot/conf:/etc/letsencrypt
# - ./certbot/logs:/var/log/letsencrypt
# - ./html/mastodon:/var/www/html
# networks:
# - internal_network
# - external_network
mailserver:
image: docker.io/mailserver/docker-mailserver:latest
container_name: mailserver
hostname: mail
domainname: molaguay.xyz
env_file: mailserver.env
ports:
- "25:25"
- "143:143"
- "587:587"
- "993:993"
volumes:
- ./certbot/conf:/tmp/certs
- ./html:/var/www/html
- ./mail/dms/mail-data/:/var/mail/
- ./mail/dms/mail-state/:/var/mail-state/
- ./mail/dms/mail-logs/:/var/log/mail/
- ./mail/dms/config/:/tmp/docker-mailserver/
- /etc/localtime:/etc/localtime:ro
environment:
- ENABLE_SPAMASSASSIN=1
- SPAMASSASSIN_SPAM_TO_INBOX=1
- ENABLE_CLAMAV=1
- ENABLE_FAIL2BAN=1
- ENABLE_POSTGREY=1
- ENABLE_SASLAUTHD=0
- ONE_DIR=1
cap_add:
- NET_ADMIN
restart: always
networks:
- internal_network
- external_network
deploy:
resources:
limits:
cpus: '0.50'
memory: 1024M
reservations:
cpus: '0.25'
memory: 512M
postgresql:
container_name: postgresql
image: postgres:13-alpine
env_file: database.env
restart: always
shm_size: 256mb
healthcheck:
test: ['CMD', 'pg_isready', '-U', 'postgres']
ports:
- 5432:5432
volumes:
- ./mastodon/postgresql:/var/lib/postgresql/data
networks:
- internal_network
redis:
container_name: redis
image: redis:7
restart: always
healthcheck:
test: ['CMD', 'redis-cli', 'ping']
volumes:
- ./mastodon/redis:/data
networks:
- internal_network
redis-volatile:
container_name: redis-volatile
image: redis:7
restart: always
healthcheck:
test: ['CMD', 'redis-cli', 'ping']
networks:
- internal_network
elasticsearch:
deploy:
resources:
limits:
cpus: '0.50'
memory: 512M
reservations:
cpus: '0.25'
memory: 128M
container_name: elasticsearch
image: elasticsearch:7.17.3
restart: always
env_file: database.env
environment:
- cluster.name=elasticsearch-mastodon
- discovery.type=single-node
- bootstrap.memory_lock=true
- xpack.security.enabled=true
- ingest.geoip.downloader.enabled=false
ulimits:
memlock:
soft: -1
hard: -1
healthcheck:
test: ["CMD-SHELL", "nc -z elasticsearch 9200"]
volumes:
- ./mastodon/elasticsearch:/usr/share/elasticsearch/data
networks:
- internal_network
backend:
container_name: backend
image: tootsuite/mastodon:v4.0.2
env_file:
#- application.env
- database.env
command: bash -c "bundle exec rails s -p 3000"
restart: always
depends_on:
- postgresql
- redis
- redis-volatile
- elasticsearch
ports:
- 3000:3000
networks:
- internal_network
- external_network
healthcheck:
test: ['CMD-SHELL', 'wget -q --spider --proxy=off localhost:3000/health || exit 1']
volumes:
- ./mastodon/uploads:/opt/mastodon/public/system
shell:
container_name: shell
image: tootsuite/mastodon:v4.0.2
env_file:
#- application.env
- database.env
command: /bin/bash
restart: "no"
networks:
- internal_network
- external_network
volumes:
- ./mastodon/uploads:/opt/mastodon/public/system
streaming:
container_name: streaming
image: tootsuite/mastodon:v4.0.2
env_file:
#- application.env
- database.env
command: node ./streaming
restart: always
depends_on:
- postgresql
- redis
- redis-volatile
- elasticsearch
ports:
- '127.0.0.1:4000:4000'
networks:
- internal_network
- external_network
healthcheck:
test: ['CMD-SHELL', 'wget -q --spider --proxy=off localhost:4000/api/v1/streaming/health || exit 1']
sidekiq:
container_name: sidekiq
image: tootsuite/mastodon:v4.0.2
env_file:
#- application.env
- database.env
command: bundle exec sidekiq
restart: always
depends_on:
- postgresql
- redis
- redis-volatile
- backend
networks:
- internal_network
- external_network
healthcheck:
test: ['CMD-SHELL', "ps aux | grep '[s]idekiq\ 6' || false"]
volumes:
- ./mastodon/uploads:/opt/mastodon/public/system
networks:
external_network:
driver: bridge
internal_network:
internal: true
docker-compose down && docker-compose up -d
docker-compose -f docker-compose.yml run --rm shell bundle exec rake secret docker-compose -f docker-compose.yml run --rm shell bundle exec rake secret docker-compose -f docker-compose.yml run --rm shell bundle exec rake mastodon:webpush:generate_vapid_key
Con dos rake secret ya tenemos el valor del SECRET_KEY_BASE y OTP_SECRET
RAILS_ENV=production NODE_ENV=production LOCAL_DOMAIN=mastodon.piensoluegoinstalo.com SINGLE_USER_MODE=false RAILS_SERVE_STATIC_FILES=false WEB_CONCURRENCY=2 MAX_THREADS=5 DEFAULT_LOCALE=es SMTP_SERVER=mastodon.piensoluegoinstalo.com SMTP_PORT=587 SMTP_LOGIN=mastodon@mastodon.piensoluegoinstalo.com SMTP_PASSWORD=mypassword SMTP_AUTH_METHOD=plain SMTP_OPENSSL_VERIFY_MODE=none SMTP_ENABLE_STARTTLS=auto SMTP_FROM_ADDRESS=mastodon@mastodon.piensoluegoinstalo.com SECRET_KEY_BASE=ed9030e6d75daa324c98fc5e6c1cc1a00aa1737dfee54d67c388848544483d8781688a52aa83ace1d69b8dc7991956b50a20ea417c700c84d7e725da4f8d4a0e OTP_SECRET=1bcccde358834299f3b6dc1d76ea4d2c9f7c662f2e65052d3b2122e2b7cb2dcc005eb96ebe156c2a1cd685cffa505f824bc039105c38d2cab7c1e38fcae15931 VAPID_PRIVATE_KEY=pnw0y4Um3sDhzwFPo6dKwZ13rf3mdS9hShOAM3bt4EY= VAPID_PUBLIC_KEY=BATAetlRA48aU6XbXdtcj1Ccx9xciO5ubnb0jJTfDtKYJ6kf8JKm2pQD0xq8jbotLcqHxN-YFaRo_5BsGSKABts=
6. Desplegar la web de Mastodon
Extraer los archivos estaticos web
docker run --rm -v /root/docker-server/mastodon/web/public:/web -u root tootsuite/mastodon:v4.0.2 bash -c "cp -r /opt/mastodon/public/* /web/"
Ahora volvamos a la configuracion de nginx
map $http_upgrade $connection_upgrade {
default upgrade;
'' close;
}
upstream backend {
server backend:3000 fail_timeout=0;
}
upstream streaming {
server streaming:4000 fail_timeout=0;
}
proxy_cache_path /var/cache/nginx levels=1:2 keys_zone=CACHE:10m inactive=7d max_size=1g;
server {
listen 80;
server_name mastodon.piensoluegoinstalo.com;
location / { return 301 https://$host$request_uri; }
}
server {
listen 443 ssl http2;
server_name mastodon.piensoluegoinstalo.com;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers HIGH:!MEDIUM:!LOW:!aNULL:!NULL:!SHA;
ssl_prefer_server_ciphers on;
ssl_session_cache shared:SSL:10m;
ssl_session_tickets off;
ssl_certificate /etc/nginx/ssl/live/mastodon.piensoluegoinstalo.com/fullchain.pem;
ssl_certificate_key /etc/nginx/ssl/live/mastodon.piensoluegoinstalo.com/privkey.pem;
keepalive_timeout 70;
sendfile on;
client_max_body_size 80m;
root /opt/mastodon/web/public;
gzip on;
gzip_disable "msie6";
gzip_vary on;
gzip_proxied any;
gzip_comp_level 6;
gzip_buffers 16 8k;
gzip_http_version 1.1;
gzip_types text/plain text/css application/json application/javascript text/xml application/xml application/xml+rss text/javascript image/svg+xml image/x-icon;
add_header Strict-Transport-Security "max-age=31536000" always;
location / {
try_files $uri @proxy;
}
location ~ ^/(system/accounts/avatars|system/media_attachments/files) {
add_header Cache-Control "public, max-age=31536000, immutable";
add_header Strict-Transport-Security "max-age=31536000" always;
root /opt/mastodon/;
try_files $uri @proxy;
}
location ~ ^/(emoji|packs) {
add_header Cache-Control "public, max-age=31536000, immutable";
add_header Strict-Transport-Security "max-age=31536000" always;
try_files $uri @proxy;
}
location /sw.js {
add_header Cache-Control "public, max-age=0";
add_header Strict-Transport-Security "max-age=31536000" always;
try_files $uri @proxy;
}
location @proxy {
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header Proxy "";
proxy_pass_header Server;
proxy_pass http://backend;
proxy_buffering on;
proxy_redirect off;
proxy_http_version 1.1;
proxy_set_header Upgrade $http_upgrade;
proxy_set_header Connection $connection_upgrade;
proxy_cache CACHE;
proxy_cache_valid 200 7d;
proxy_cache_valid 410 24h;
proxy_cache_use_stale error timeout updating http_500 http_502 http_503 http_504;
add_header X-Cached $upstream_cache_status;
add_header Strict-Transport-Security "max-age=31536000" always;
tcp_nodelay on;
}
location /api/v1/streaming {
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header Proxy "";
proxy_pass http://streaming;
proxy_buffering off;
proxy_redirect off;
proxy_http_version 1.1;
proxy_set_header Upgrade $http_upgrade;
proxy_set_header Connection $connection_upgrade;
tcp_nodelay on;
}
error_page 500 501 502 503 504 /500.html;
}
Descomentamos el application.env
version: "3.8"
services:
nginx:
container_name: nginx
image: nginx:latest
restart: unless-stopped
ports:
- 80:80
- 443:443
volumes:
- ./nginx/conf:/etc/nginx/conf.d
- ./certbot/conf:/etc/nginx/ssl
- ./html:/var/www/html
networks:
- internal_network
- external_network
# mastodoncertbot:
# container_name: mastodoncertbot
# image: certbot/certbot:latest
# command: certonly --webroot --webroot-path=/var/www/html --email adriandepalma@hotmail.es --agree-tos --no-eff-email -d mastodon.piensoluegoinstalo.com
# volumes:
# - ./certbot/conf:/etc/letsencrypt
# - ./certbot/logs:/var/log/letsencrypt
# - ./html/mastodon:/var/www/html
# networks:
# - internal_network
# - external_network
mailserver:
image: docker.io/mailserver/docker-mailserver:latest
container_name: mailserver
hostname: mail
domainname: molaguay.xyz
env_file: mailserver.env
ports:
- "25:25"
- "143:143"
- "587:587"
- "993:993"
volumes:
- ./certbot/conf:/tmp/certs
- ./html:/var/www/html
- ./mail/dms/mail-data/:/var/mail/
- ./mail/dms/mail-state/:/var/mail-state/
- ./mail/dms/mail-logs/:/var/log/mail/
- ./mail/dms/config/:/tmp/docker-mailserver/
- /etc/localtime:/etc/localtime:ro
environment:
- ENABLE_SPAMASSASSIN=1
- SPAMASSASSIN_SPAM_TO_INBOX=1
- ENABLE_CLAMAV=1
- ENABLE_FAIL2BAN=1
- ENABLE_POSTGREY=1
- ENABLE_SASLAUTHD=0
- ONE_DIR=1
cap_add:
- NET_ADMIN
restart: always
networks:
- internal_network
- external_network
deploy:
resources:
limits:
cpus: '0.50'
memory: 1024M
reservations:
cpus: '0.25'
memory: 512M
postgresql:
container_name: postgresql
image: postgres:13-alpine
env_file: database.env
restart: always
shm_size: 256mb
healthcheck:
test: ['CMD', 'pg_isready', '-U', 'postgres']
ports:
- 5432:5432
volumes:
- ./mastodon/postgresql:/var/lib/postgresql/data
networks:
- internal_network
redis:
container_name: redis
image: redis:7
restart: always
healthcheck:
test: ['CMD', 'redis-cli', 'ping']
volumes:
- ./mastodon/redis:/data
networks:
- internal_network
redis-volatile:
container_name: redis-volatile
image: redis:7
restart: always
healthcheck:
test: ['CMD', 'redis-cli', 'ping']
networks:
- internal_network
elasticsearch:
deploy:
resources:
limits:
cpus: '0.50'
memory: 512M
reservations:
cpus: '0.25'
memory: 128M
container_name: elasticsearch
image: elasticsearch:7.17.3
restart: always
env_file: database.env
environment:
- cluster.name=elasticsearch-mastodon
- discovery.type=single-node
- bootstrap.memory_lock=true
- xpack.security.enabled=true
- ingest.geoip.downloader.enabled=false
ulimits:
memlock:
soft: -1
hard: -1
healthcheck:
test: ["CMD-SHELL", "nc -z elasticsearch 9200"]
volumes:
- ./mastodon/elasticsearch:/usr/share/elasticsearch/data
networks:
- internal_network
backend:
container_name: backend
image: tootsuite/mastodon:v4.0.2
env_file:
- application.env
- database.env
command: bash -c "bundle exec rails s -p 3000"
restart: always
depends_on:
- postgresql
- redis
- redis-volatile
- elasticsearch
ports:
- 3000:3000
networks:
- internal_network
- external_network
healthcheck:
test: ['CMD-SHELL', 'wget -q --spider --proxy=off localhost:3000/health || exit 1']
volumes:
- ./mastodon/uploads:/opt/mastodon/public/system
shell:
container_name: shell
image: tootsuite/mastodon:v4.0.2
env_file:
- application.env
- database.env
command: /bin/bash
restart: "no"
networks:
- internal_network
- external_network
volumes:
- ./mastodon/uploads:/opt/mastodon/public/system
streaming:
container_name: streaming
image: tootsuite/mastodon:v4.0.2
env_file:
- application.env
- database.env
command: node ./streaming
restart: always
depends_on:
- postgresql
- redis
- redis-volatile
- elasticsearch
ports:
- '127.0.0.1:4000:4000'
networks:
- internal_network
- external_network
healthcheck:
test: ['CMD-SHELL', 'wget -q --spider --proxy=off localhost:4000/api/v1/streaming/health || exit 1']
sidekiq:
container_name: sidekiq
image: tootsuite/mastodon:v4.0.2
env_file:
- application.env
- database.env
command: bundle exec sidekiq
restart: always
depends_on:
- postgresql
- redis
- redis-volatile
- backend
networks:
- internal_network
- external_network
healthcheck:
test: ['CMD-SHELL', "ps aux | grep '[s]idekiq\ 6' || false"]
volumes:
- ./mastodon/uploads:/opt/mastodon/public/system
networks:
external_network:
driver: bridge
internal_network:
internal: true
Con todo listo vamos a popular la bases de datos
docker-compose -f docker-compose.yml up -d postgresql redis redis-volatile docker-compose -f docker-compose.yml run --rm shell bundle exec rake db:setup docker-compose -f docker-compose.yml run --rm shell bundle exec rake db:migrate
Una vez con las bases de datos en pie ya podemos crear el usuario administrador del server.
docker-compose down && docker-compose up -d docker-compose -f docker-compose.yml run --rm shell bin/tootctl accounts create godofserver --email mastodon@mastodon.piensoluegoinstalo.com --confirmed --role Owner
Si recibes un mail es que todo ha ido ha ido bien.
Y eso es todo ya tenemos un servidor mastodon en el dominio https://mastodon.piensoluegoinstalo.com


0 comentarios